Once upon a time, piracy was easy to spot. A skiff on the horizon, men with rifles, and a demand for ransom delivered with all the subtlety of a foghorn. Crude, dangerous, but at least visible.
Fast forward to 2025, and the pirates don’t need boats anymore — just decent WiFi and a cheap laptop.
The real hijacker today might be sitting thousands of miles away, never having smelled saltwater. Instead of boarding your vessel, they send a phishing email — “click here for crew welfare benefits” — and suddenly they’re not just in your inbox, they’re in your systems.
Welcome to the age of digital piracy — and the rising reality of maritime cyber threats that no naval frigate can stop.
“It’s a pattern we’ve covered before — smart ships with the same old headlines, just with newer failure modes.”
Maritime Cyber Threats: Ransomware as the New Boarding Party
In 2017, Maersk was brought to a standstill by the NotPetya cyberattack. Terminals shut down. Booking systems collapsed. Cargo tracking disappeared into the void. Estimated losses? Hundreds of millions of dollars.
Not a single pirate boarded a ship.
Since then, maritime cyber threats have made port infrastructure an increasingly attractive target. The Port of Antwerp has previously dealt with criminal groups infiltrating terminal systems to manipulate container movements for illicit cargo. Across the Atlantic, major ports like Port of Houston have reported repeated cyber intrusion attempts on operational systems.
This isn’t cinematic piracy. It’s quieter. More precise. And often more disruptive.
Because unlike a hijacked vessel, you can’t escort a compromised server back to safety with a naval frigate.
Onboard threats: Your ECDIS is only as good as its last update
Onboard maritime cyber threats are less dramatic — but just as real.
- ECDIS vulnerabilities: While modern systems are increasingly secured, outdated configurations and poor patch management can leave gaps. Manipulation isn’t common — but it’s possible under the right conditions.
- GPS interference: Jamming and spoofing incidents have been documented in high-risk regions, particularly near conflict zones and congested waterways. When positioning becomes unreliable, so does decision-making.
- Human entry points: The most consistent vulnerability remains the crew. USB devices, unsecured WiFi, or phishing emails continue to be the easiest way into otherwise protected systems.
And yes, some vessels are still running legacy operating environments that would make an IT auditor quietly resign.
Nothing says “cutting-edge navigation” like protecting mission-critical systems with software older than your cadet.
Insurance and liability: Whose mess is this anyway?
Here’s where the industry gets uncomfortable.
Traditional marine risks are well defined. Piracy? Covered. Fire? Covered. Grounding? Covered.
Maritime cyber threats? That’s where clarity starts to evaporate.
If a ransomware attack disrupts reefer containers, leading to cargo loss — who pays?
The cargo owner? The operator? The terminal? The insurer who quietly excluded cyber risk in the fine print?
Even General Average, one of shipping’s oldest principles, struggles in this space. It was designed for physical sacrifices — not digital failures originating in a data centre halfway across the world.
The result? A growing grey zone where operational risk moves faster than contractual clarity.
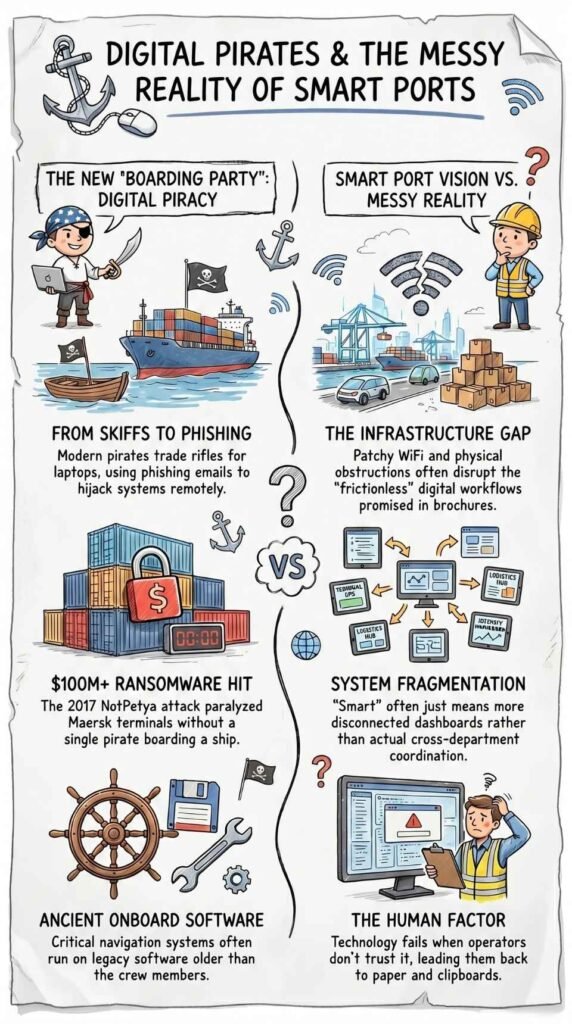
Smart ports: When your harbour gets WiFi but not common sense
“Smart ports” are the industry’s favourite buzzword.
Automation. AI-driven logistics. Blockchain-enabled documentation. Predictive maintenance. On paper, it’s flawless — a seamless, frictionless ecosystem.
In reality? It’s more… human.
Yes, there are real gains:
- Smarter berth allocation reducing idle time
- Automated yard systems improving efficiency
- Digital documentation reducing paperwork delays
- Data-driven maintenance improving asset uptime
But shipping has a unique talent for turning elegant systems into operational theatre.
We’ve called this out before as the digital delusion in the shipping industry — elegant on paper, messy at the terminal.
The messy reality of smart ports
- Infrastructure gaps: A port is only as “smart” as its weakest connection. Network reliability, legacy systems, and physical obstructions still disrupt digital workflows more often than brochures admit.
- Cyber exposure at scale: A vessel can be isolated. A port cannot. A successful attack on terminal systems can disrupt thousands of containers simultaneously — amplifying both financial and operational impact.
- Fragmented systems: True integration remains rare. Shipping lines, terminals, customs, and agents often operate on parallel systems. “Smart” sometimes just means more dashboards, not better coordination.
- Human adoption: Technology doesn’t fail — implementation does. If operators don’t trust or understand the system, they revert to what works. Often, that’s still a clipboard.
Because at the end of the day, the most reliable backup system in shipping is still… a human being who’s seen it go wrong before.
Digital credentials: No more paper certs, please
For decades, maritime compliance has been defined by paper — certificates, endorsements, stamps, signatures.
Lose one, and it becomes an operational emergency.
Now, the industry is moving toward digital seafarer certification. In theory, it solves everything: faster verification, reduced fraud, streamlined administration.
In practice, it introduces a familiar set of challenges.
The dream vs. the deck reality
- Connectivity dependency: Digital systems assume availability. Ships operate in environments where connectivity is still inconsistent.
- Cyber risk shift: Forgery risk decreases — but system vulnerability increases. The threat doesn’t disappear. It evolves.
- Regulatory fragmentation: Not all flag states move at the same pace. Recognition and interoperability remain ongoing challenges.
- User trust: Many seafarers still trust what they can physically verify. Digital trust takes time — and consistency — to build.
Fraud-proof… until it’s not
Digital verification systems will likely reduce document fraud significantly.
But no system is immune.
As digital ecosystems expand, so does the attack surface. And with increasing integration comes a new question: where does verification end, and monitoring begin?
Because once credentials, training records, and performance metrics are connected, the line between compliance and oversight can blur.
The way forward
Digitalisation is not optional. It’s already happening and maritime cyber threats are evolving faster than most contracts can keep up with.
The real question is whether it’s implemented with operational reality in mind — or imposed as a top-down solution disconnected from life at sea.
If systems are built for efficiency onshore but ignore usability offshore, the result won’t be transformation. It’ll be resistance.
What we can learn from others
Sectors like aviation and defense have already developed robust digital certification ecosystems — secure, verifiable, and widely accepted.
The key difference? They prioritised the end-user.
Shipping can do the same — if it chooses to design with empathy, not just efficiency.
Because digitalisation without usability is just bureaucracy… with better fonts.
The last paper chase
Paper is fading. That much is inevitable.
Digital systems will define the next phase of maritime operations — from ports to vessels to people.
But technology alone doesn’t create trust. Implementation does.
And in an industry built on experience, instinct, and judgment, the human factor remains the most critical system of all.
Because at the end of the day, the best credential a seafarer can hold…
is still the one nobody needs to question.
📌 Has your vessel or port ever dealt with a cyber incident — directly or indirectly?
Where did the real failure happen: technology, process, or people?